Our cybersecurity team has received more than a dozen notifications from local law firms that have had their email accounts compromised in the last two weeks. We feel it is our duty to notify our business community of the recent wave of attacks.
Below is an example of the message being sent out by the affected accounts.
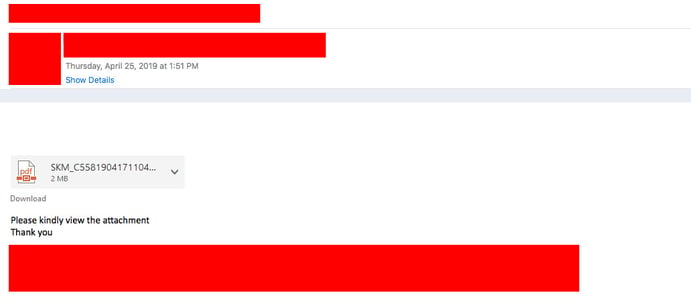
The emails are very deceiving. Since the email account is compromised and the attacker has the login credentials, the emails appear to come directly from the affected account owner. After a quick analysis from our team, this attack is likely a dual threat. If you click the link you will be directed to a webpage asking for your login credentials so that hacker can use them to login to your account directly. Additionally, when you click the link, a large number of files are downloaded to the local machine without your knowledge including tools that are commonly used by these hackers to exploit your network. Unfortunately, in this case it is not likely safe to assume that if you didn’t enter your credentials that you are safe. You should be aware that additional measures should be taken by your firm to safeguard the firm's critical systems and data.
Please, notify your colleagues of this attack. If you believe your firm may have been compromised, please know that we are available to help navigate this issue.
If you are more tech savvy, please see a brief description from our team below. You may also look at the details of this attack from our sandbox here:https://www.hybrid-analysis.com/sample/059e2bb876ccf92fc8912fd89d06e9f7fa55bebed5e7364e80d1e7d757e8a231/5cc21da10388386258fc871d
“A phishing campaign was seen using a PDF document that directed users to a landing page that was made to look like a OneDrive account login. Once the link was clicked it sent users to a fake landing page and asked users to enter credentials to view the PDF. Further analysis shows that there were 0 malicious signatures found so the file will most likely slip through any antivirus detections. 48 domains and IP addresses are reached out to once the link is clicked on, and at least 1 IP obtained during analysis shows an oversea connection to the EU. Classification for this attachment and link are phishing with the possibility of a Trojan. This can be seen in the behavior as 320 files are dropped on to the system without the user’s knowledge. Below is the link that the attachment sends you to, please note https has been changed to hXXps.
hXXps://onedrive.live.com/?authkey=%21AOfJ4VOckKKx94Y&cid=2C58A4EFD27D59FA&id=2C58A4EFD27D59FA%21112&parId=root&o=OneUp “

