An attacker leveraged a combination of Microsoft Exchange vulnerabilities (ProxyShell), which led to the deployment of Lockbit 2.0 ransomware. Here's what happened:
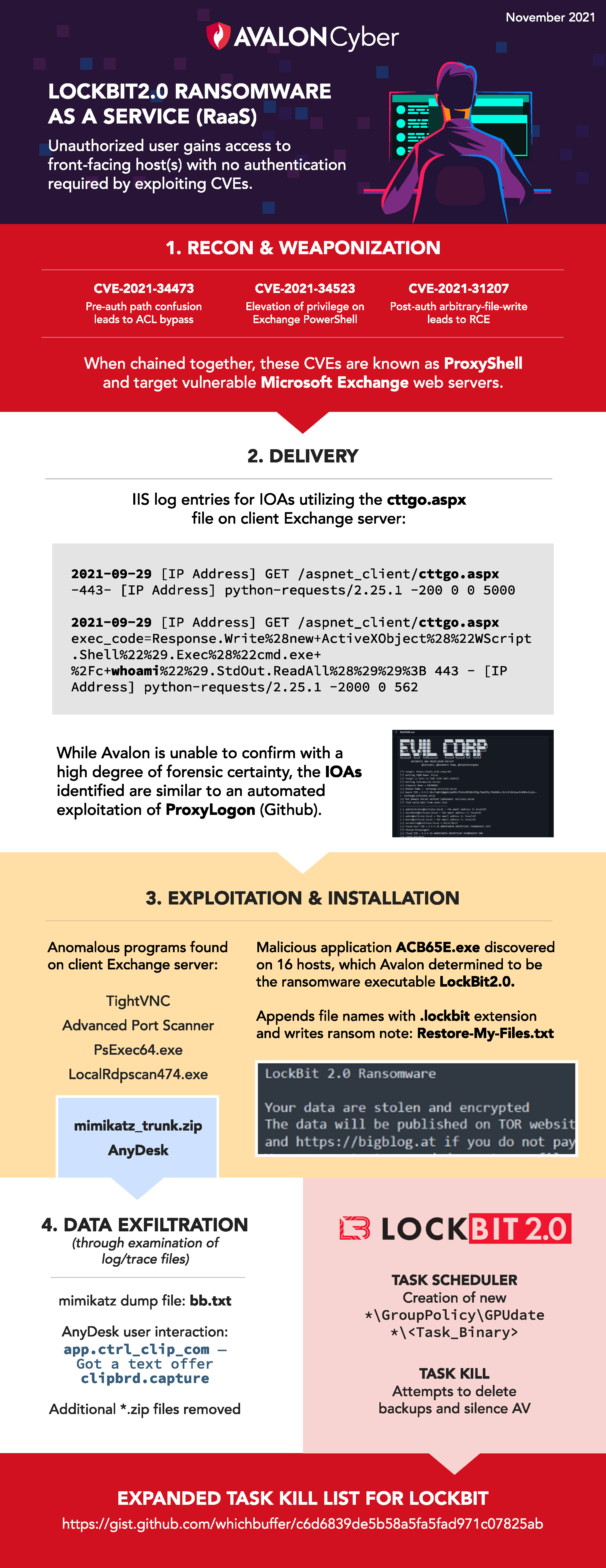
If you suspect ransomware or experience any type of cyber incident, call our Incident Response number at 1.877.216.2511 or, if you have any questions for our cybersecurity experts, feel free to contact us online.